Automation vendors develop great products and services. They excel at leveraging the latest technological developments to solve the problems facing industries they work in. After creating a vision for the future, vendors put a lot of effort into communicating it to the market.
Much of this communciation is educational, and used by many to stay up to date with automation industry trends and opportunities for improvement. Understanding what is possible allows owners of factories, plants and facilicities to plan investment and stay up to date with technological developments.
But does what they’re recommending fit into your strategy and address your problems?
Take Integrated Control and Safety Systems (ICSS).
If you’re not familiar, this is the concept of sourcing all control and safety systems from one supplier in a fully integrated package.
A big market for ICSS is the oil & gas industry, where safety (shutdown) systems can be as large and complex as the process control systems they supervise. Here the benefits typically cited by vendors make installing an ICSS solution very appealing:
- Simplified system/network architecture
- Fast and efficient communications between control and safety systems
- Cost savings from reduction in required spares (thanks to common hardware) and engineering hours (standard programming and maintenance interfaces)
- Increased visibility of safety system information
- Ability to avoid duplicating functionality (process data read by safety equipment can easily be used for process control)
- Single supplier for all programmable automation equipment
- The list goes on…
ICSS’s are, of course, good for automation vendors too. By increasing their scope of supply they can push out competitors, and have a larger ‘installed base’ to offer service and support packages on. It would seem a win-win …
Except, something else is very important to the oil & gas industry: cyber security. In particular the risk associated with losing control while integrity of the emergency shutdown system is also compromised. Security incidents in recent years have led several oil majors to review their ICSS architectures and put additional measures in place to address this risk.
When writing this article I couldn’t find a single vendor website which mentioned cyber security on the page explaining their ICSS solution.
I’m not saying ICSSs are insecure or claims their manufacturers make are untrue.
I am saying it pays to test solutions against your own strategy, requirements and risk appetite.
End-users tend to focus more on reducing initial project costs than lifecycle ownership costs. They can control the (competitive) project tendering process, but have little purchasing power when buying spare parts from a (sole) supplier. This leads automation vendors to use higher-margin service revenue to recover profit lost during projects.
Understanding and avoiding the potential pitfalls of recommended solutions is crucial to building infrastructure which supports, rather than undermines, your long-term strategy. Suppliers will always be happy to save you time and money early on by using ‘tried and testeed’ or ‘standard’ solutions - they know it’ll pay them in the long-term.
This doesn’t only apply to highly automated and integrated companies. How many machine suppliers now build a facility for remote access into their equipment? Who owns the data, taken from your plant, driving the web portal you use to monitor energy consumption? I could go on.
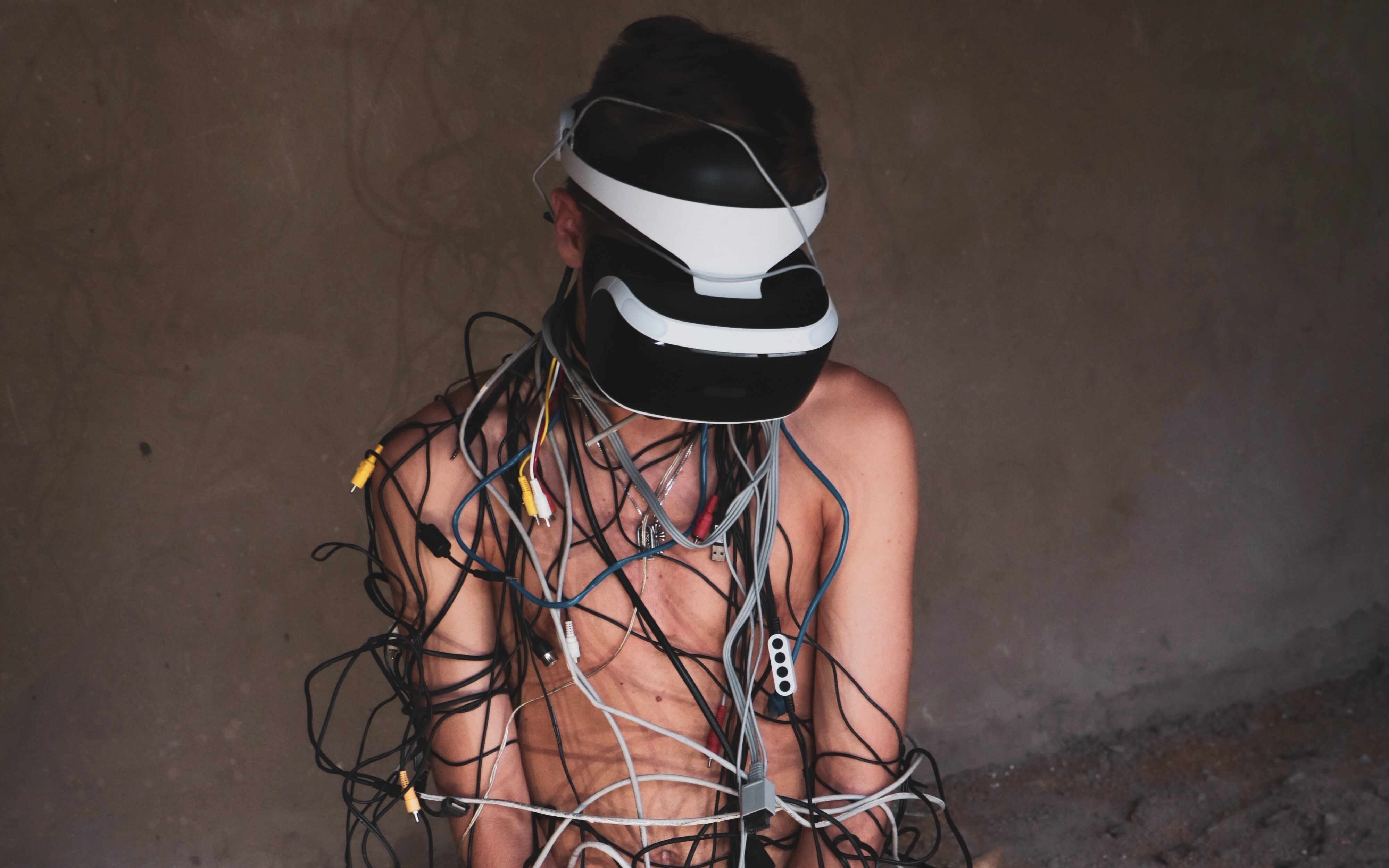
Treat the future vision presented by suppliers with healthy scepticism. Ensuring you fully understand the long-term implications of competing designs and approaches will ensure you don’t end up living someone else’s future.